Mercor Data Breach: What a $10B Unicorn Teaches About Trust
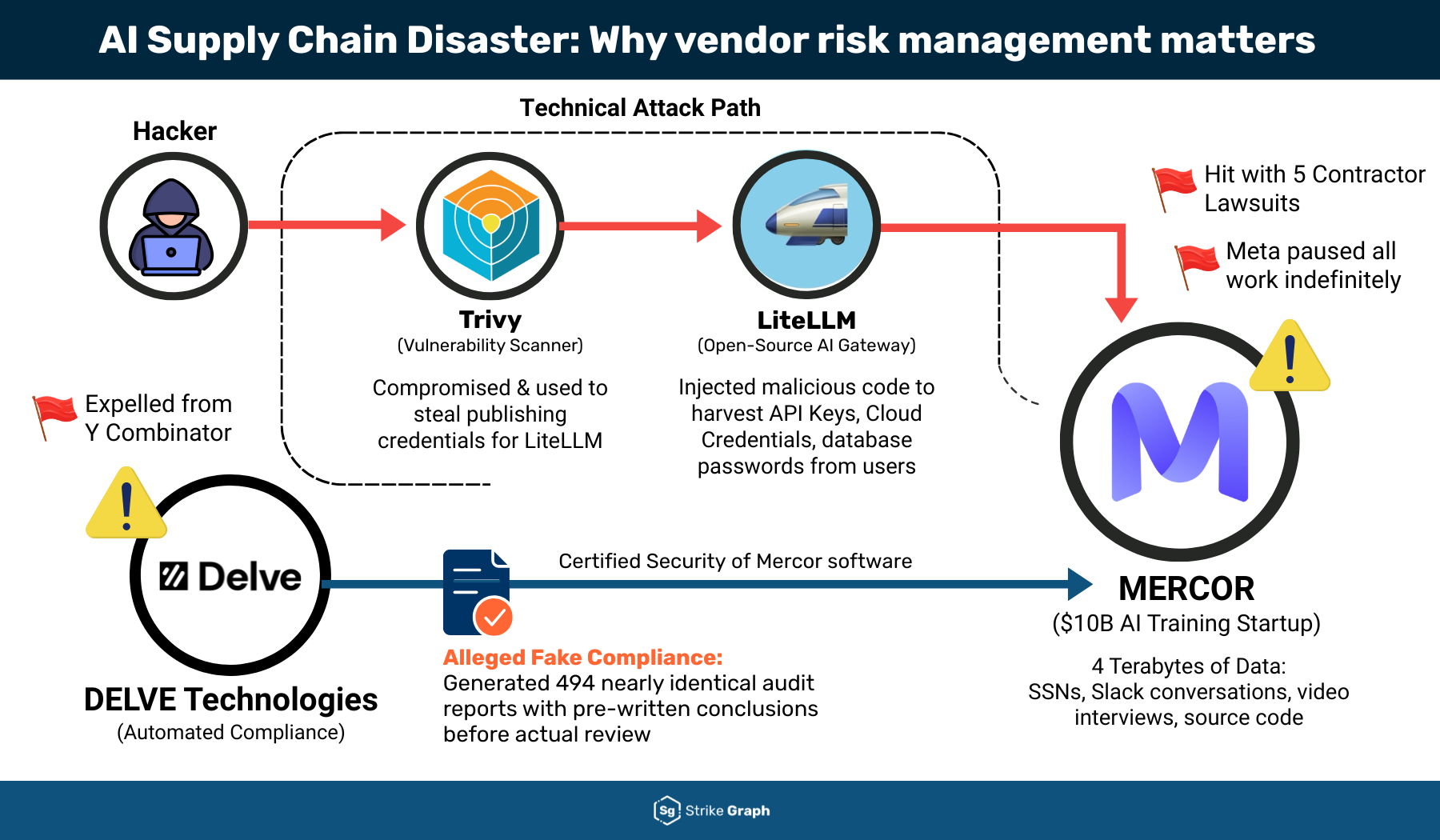
Mercor, the $10 billion hiring platform, is reeling from a data breach that exposed candidate info and rattled enterprise buyers. You feel this one because it shows how thin the ice is for AI startups that trade on trust. The Mercor data breach did not just leak resumes. It undercut the promise that AI hiring tools are safer and faster than traditional recruiters. Why does this matter now? Investors are still pouring money into similar platforms, and your own stack likely relies on third-party AI tools with similar architectures. The lesson: security debt compounds faster than user growth, and the market is suddenly paying attention.
Fast Facts You Need Now
- Mercor disclosed the breach after researchers surfaced exposed buckets tied to candidate profiles.
- Customers report delayed incident notices, raising compliance questions.
- The company paused some matching features while auditing models and access logs.
- Regulators in the EU and California are already asking about GDPR and CPRA exposure.
Mercor Data Breach Fallout: What Actually Happened
I read the filings and investor notes. The breach came from misconfigured cloud storage tied to an internal analytics pipeline, not an exotic zero-day. Credentials were reused across staging and production, which let an attacker pivot. Think of leaving your restaurant’s back door open while the front has cameras. Attackers scraped names, emails, work histories, and recruiter notes. No payment data, but plenty of material for spear phishing. One single-sentence paragraph lives here.
Security is not a feature you bolt on after the Series C; it is the core product when your product is data.
Who trusts a unicorn that leaks resumes? Enterprises now ask for SOC 2 refreshes and real-time audit trails before signing renewals. That slows revenue recognition and churn risk climbs. The ripple hits every AI vendor selling to HR.
How To Respond When Your AI Vendor Stumbles
You cannot wait for Mercor to finish its postmortem. Protect your side first. Rotate API keys, tighten SSO scopes, and reroute logs to your SIEM for at least 30 days. Treat recruiter inboxes as high-risk because phishing will spike. If you mirror candidate data into your own data lake, check access policies and run fresh scans for exposed PII.
Checklist for Security Teams
- Pull vendor access logs and review anomalies over the last 45 days.
- Force MFA resets for all recruiter and hiring manager accounts.
- Set conditional access rules that quarantine logins from new locations.
- Update your privacy notice to reflect shared data flows with Mercor.
- Brief legal on breach timelines to align on notification duties.
Think of this as tuning a racing bike before a climb. Every loose cable slows you down and can throw you off the course.
What Mercor Should Do Next
Mercor needs to publish a timeline, rotate every shared secret, and split staging from production completely. Privacy regulators look for rapid containment and user notice within statutory windows. Slow responses invite fines and class actions. The company also needs to prove that its matching models no longer have access to raw identifiers during training. Without that, claims about privacy-by-design ring hollow.
Here is the thing: speed matters, but clarity matters more. A crisp FAQ, live status page, and verifiable controls (like signed attestations from cloud providers) rebuild some trust. And the board should tie executive compensation to security milestones. That signals priorities to the market.
Mercor Data Breach Lessons for Every Founder
Founders love to say they are product-led. Security is part of the product. Invest early in secrets management, environment isolation, and tabletop exercises that include your comms lead. Use third-party attack surface monitoring to spot exposed buckets before a researcher does. Budget for a privacy counsel who understands both GDPR and AI model governance.
Why wait for a headline to prove you need this? You would not roll out a new feature without tests. Apply the same discipline to access control and incident drills.
Looking Ahead
Mercor will survive if it treats this breach as a seismic reset, not a PR issue. The broader AI hiring market will now face deeper vendor due diligence, and that is healthy. Expect procurement teams to ask for continuous compliance evidence, not annual PDFs. If you build in this space, adopt that standard now. Will the next unicorn learn faster?
/socialsamosa/media/media_files/2025/11/03/fi-all-templates-4-2025-11-03-14-08-44.jpg)